Cybersecurity Alphabet Soup
A Primer on Cybersecurity Frameworks
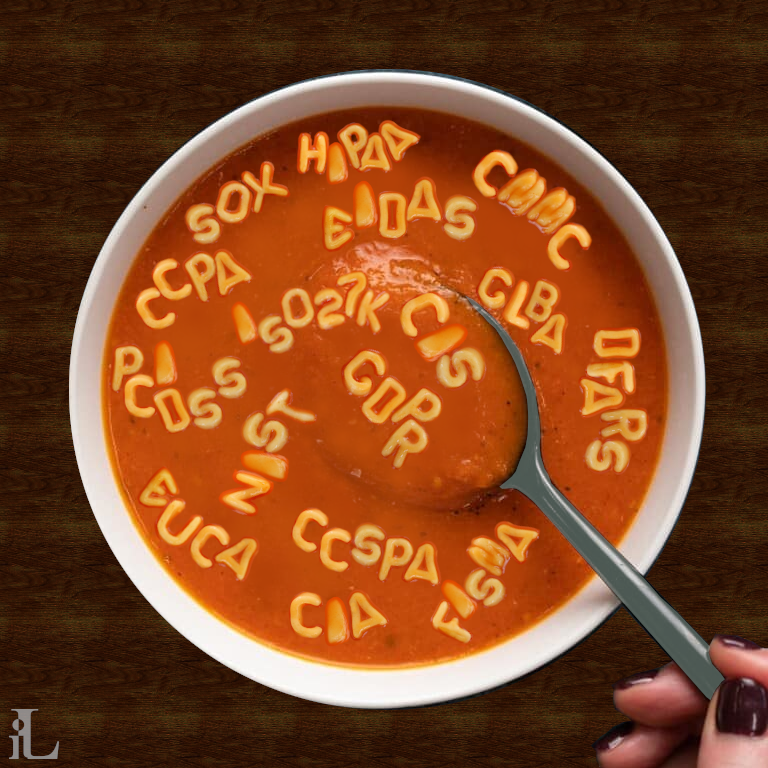
The world of cybersecurity is confusing enough without the alphabet soup of acronyms that are used to describe the various frameworks, standards, and regulations that exist. In this article we provide a brief overview of some of the more common frameworks, regulations and standards, and how they relate to each other. It is not intended to be an exhaustive list of all frameworks and standards, nor is it intended to be a comprehensive description of the regulations mentioned. Think of it as an illustration of what acronyms relate to what security concepts such as privacy, risk, and governance.
The first thing to understand is that there are two main types of frameworks: those that are prescriptive and those that are supportive. Prescriptive frameworks are those that tell you what to do, and are usually enforceable by some formal body. Supportive frameworks are frameworks that the cybersecurity community has developed as a means to satisfy regulations and to support an organization's efforts to protect against cyber threats and threat actors.
Prescriptive Frameworks
Prescriptive frameworks include regulations and standards. Regulations are laws that are enforceable by (usually) a government body. Standards are not laws, but are often referenced in regulations and are enforceable by the organization that has adopted them. The following are some of the more common regulations:
- Health Insurance Portability and Accountability Act (HIPAA)
- General Data Protection Regulation (GDPR)
- Payment Card Industry Data Security Standard (PCI DSS)
- California Consumer Privacy Act (CCPA)
- Personal Information Protection and Electronic Documents Act (PIPEDA)
The above regulations may reference certain standards, but they do not all require adherence to a given standard. The ISO 27001 standard is a good example of a standard that is referenced by many regulations. The following are some of the more common standards:
- International Organization for Standardization (ISO) 27001
- Control Objectives for Information and Related Technologies (COBIT)
- Committee of Sponsoring Organizations of the Treadway Commission (COSO)
- Information Technology Infrastructure Library (ITIL)
- Center for Internet Security (CIS) Controls
Supportive Frameworks
What is also confusing is that some of the "standards" are in-fact Supportive Frameworks in their own right. Furthermore, some of the Supportive Frameworks are free and in the public domain (such as NIST and CIS), while others are proprietary and require the purchase of licensed access (such as ISO27K and HITRUST). The following are some of the more common Supportive Frameworks:
- National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF)
- International Organization for Standardization (ISO) 27001
- Control Objectives for Information and Related Technologies (COBIT)
- Committee of Sponsoring Organizations of the Treadway Commission (COSO)
- Information Technology Infrastructure Library (ITIL)
- Center for Internet Security (CIS) Controls
- Health Information Trust Alliance (HITRUST)
What's right for me?

It is our considered opinion that in order to choose the correct framework, one needs to understand some fundamentals about security in general, and cybersecurity in particular. The practice of security has three main pillars: Confidentiality, Integrity, and Availability. These three pillars are often referred to as the CIA triad (yes, I know... yet another acronym). Let's dig into the triad with an example from the physical world. You are invited to a party during the week, and despite your better judgement, you imbibe too much and wake up the next day with a headache. You don't want your colleagues to know how foolish you had been (confidentiality) so you decide to take some headache medicine. You reach into the medicine cabinet and find a new bottle of pills. As a good consumer, you ensure that the tamper resistant seal is intact (integrity). You put the bottle back in the cabinet, so that you can find it again when you need it (availability).
In cybersecurity, the CIA triad generally addresses the protection of information. After-all, in today's world information is a precious commodity. So confidentiality ensures that the information that you possess cannot be seen or used by those who do not have permission. Integrity ensures that the information you have remains accurate, and has not been changed or compromised by any third party... or even accidentally by you. Finally, availability ensures that when you, or other authorized individuals, need the information, it can be accessed. There remains, of course, much more to the story, however when one is considering what cybersecurity framework to employ to satisfy a particular regulation, one should read the regulation with the CIA Triad in mind. Then, when one is considering frameworks, the CIA Triad will once again help to clarify the controls they offer.
For example, the GDPR is primarily concerned with the protection of personal information. As such, it is primarily concerned with confidentiality. However, it also requires that the subject of the data has a certain degree of control over it, so integrity and availability are also important. The PCI DSS is primarily concerned with the protection of credit card information. As such, it is primarily concerned with confidentiality. The HIPAA is primarily concerned with the protection of personal health information. As such, it is primarily concerned with confidentiality but as with GDPR, integrity and availability are important because HIPAA also adresses the exchange of information. All other regulations like CCPA and PIPEDA also have varying degrees of emphasis on confidentiality, integrity, and availability.
Count the Cost
The principle of Cost-Benefit Analysis is a fundamental concept in cybersecurity and risk management, emphasizing the need to evaluate the cost of implementing a security control against the potential value of the assets it protects. There are all sorts of people willing to sell you a full certification against any one of the frameworks above... and that certification may be worth every penny. However, it is equally important to manage what is called in other industries the "Total Cost of Ownership". I am not proposing avoiding certification, what I am proposing is certify against what must be certified (as required by clients or governments) but do not paint yourself into a corner where you must now maintain a certification that does not have an external requirement. In the end, the choice of framework is a business decision that may involve extended financial commitment. Treat it with the same respect that you would any capital investment.
Conclusion
In the world of cybersecurity, there are lots of confusing acronyms. Here, we helped you understand some of the concepts behind the frameworks and rules. We also discussed the "CIA Triad" (no, it's not a spy thing!) You learned that it stands for Confidentiality, Integrity, and Availability. These three things are important in keeping information safe. You learned that Confidentiality means keeping information private, Integrity means making sure it's accurate and hasn't been changed, and Availability means being able to access it when you need it. When choosing a cybersecurity framework, think about the CIA Triad and how well the framework covers these aspects. Likewise, choosing a cybersecurity rule isn't just about following the law. It's about picking the right way for your business to do so while also managing the investment through the correct lens.